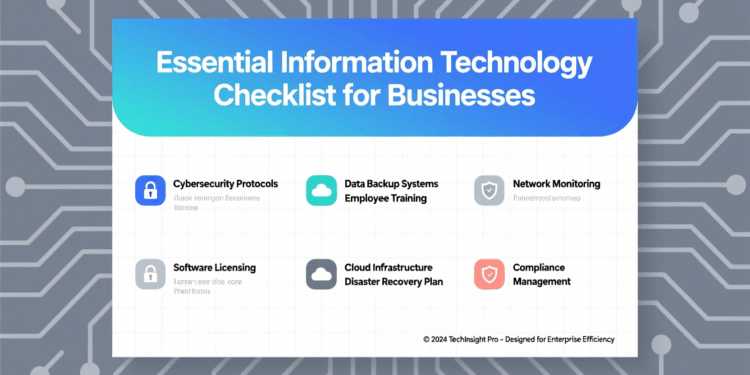
Information technology for business is no longer optional. Companies rely on IT to manage daily operations and stay competitive. Proper IT systems improve efficiency and reduce costs.
Security is a key concern, and businesses must protect their data. Cloud solutions, networks, and devices all need attention. Keeping IT up to date ensures smooth workflows and better customer service.
Explore the following points to understand the essential areas every business should focus on when managing IT.
Network Infrastructure
A strong network is the foundation of business IT. All computers and devices must connect reliably.
Use secure connections to prevent unauthorized access. Regularly check routers, switches, and cabling for issues.
Proper network planning avoids slowdowns and downtime. Backup systems should be in place for critical data.
Employees should understand basic network security practices. Monitoring traffic can identify problems early.
A solid network keeps operations consistent and safe. Test network speeds periodically to ensure efficiency.
Keep spare network equipment ready for emergencies. Document the network setup for troubleshooting and planning.
Data Backup and Recovery
Backing up data is essential for business continuity. Store backups in multiple locations to prevent loss. Test recovery processes regularly to ensure reliability. Automate backups to reduce human error.
Keep backups for the required duration by law or policy. Protect backup files with strong encryption. Limit access to backup systems to trusted personnel. Recovery plans must be documented and easy to follow.
Reliable backups reduce the impact of hardware failures or cyberattacks. Use cloud storage as a secondary backup option. Rotate backup drives to maintain integrity. Review backup procedures regularly to improve efficiency.
Cybersecurity Measures
Cybersecurity protects sensitive business information. Use strong passwords and multi-factor authentication.
Install and update antivirus and anti-malware software. Train employees to spot phishing and scams.
Monitor systems for unusual activity. Secure Wi-Fi networks from unauthorized use.
Update software regularly to fix vulnerabilities. Limit administrative access to key systems.
Consistent cybersecurity practices prevent costly breaches. Use encryption for sensitive files and communications.
Monitor third-party access for potential risks. Maintain an incident response plan for cyber threats.
Hardware Management
Businesses need the right hardware to run efficiently. Computers, servers, and peripherals should meet workload requirements.
Maintain and replace aging hardware on schedule. Keep spare parts for critical devices.
Track warranties and service agreements. Ensure proper disposal of old equipment.
Use energy-efficient devices to lower costs. Inventory hardware for accountability.
Well-maintained hardware reduces downtime and improves performance. Label and organize devices for easy identification.
Clean hardware regularly to extend its lifespan. Monitor performance to plan timely upgrades.
Software Management
Software must support business needs. Use licensed and updated applications only. Remove unused software to free resources.
Test updates before full deployment. Monitor for compatibility issues across systems.
Train staff on proper software use. Track software inventory for audits.
Implement user access controls for sensitive software. Proper software management prevents errors and security risks.
Document software procedures for consistency. Schedule regular software reviews to maintain efficiency. Keep a list of approved software for reference.
Cloud Services
Cloud solutions provide flexible IT resources. Use cloud storage to save local space. Ensure cloud services comply with security standards.
Back up cloud data regularly. Monitor usage and costs to avoid overspending.
Train staff to access cloud tools efficiently. Use cloud-based collaboration for team projects.
Review service agreements periodically. Cloud adoption increases scalability and accessibility.
Restrict access to authorized users only. Test cloud performance and reliability regularly. Keep alternative solutions ready in case of downtime.
Email Management
Email remains a key business tool. Use secure email platforms to protect communications. Archive emails for legal or operational needs. Implement spam filters to reduce distractions. Educate staff on phishing threats.
Monitor email usage for compliance. Ensure proper backup of important messages.
Set retention policies for different types of emails. Proper email management keeps communication organized and safe.
Review email storage limits to maintain performance. Train employees on proper email etiquette. Monitor attachments and links for security risks.
Mobile Device Management
Mobile devices must be managed carefully. Track company-owned phones and tablets.
Use passwords and encryption to secure data. Set up remote wipe in case of loss.
Control app installation to reduce risks. Monitor usage for security and productivity. Update devices regularly.
Limit access to sensitive company systems. Proper mobile management protects data on the go.
Define policies for personal device use. Educate employees on mobile security best practices. Audit devices periodically to ensure compliance.
User Access Control
Access control restricts sensitive information. Only give employees access to what they need.
Use role-based permissions for efficiency. Regularly review and update access rights.
Remove access immediately when employees leave. Track login attempts for unusual activity.
Require strong passwords and regular updates. Monitor privileged accounts closely.
Strong access control reduces internal and external risks. Use logs to audit user activity.
Limit default access for new accounts. Ensure temporary access is removed promptly.
IT Support and Helpdesk
IT support keeps systems running smoothly. Provide employees with clear ways to report issues.
Track support requests for resolution trends. Use ticketing systems for accountability.
Train support staff to resolve problems quickly. Maintain documentation of common solutions.
Monitor response times to ensure efficiency. Conduct regular reviews of support performance.
Reliable IT support reduces downtime and frustration. Create escalation procedures for urgent problems.
Collect feedback to improve services. Review support tools for better performance.
Software Licensing Compliance
Businesses must follow software laws. Track all licenses and renew on time. Avoid unlicensed installations to prevent fines.
Conduct audits regularly. Educate staff on proper software usage. Keep documentation of all licenses.
Remove expired or unused licenses. Ensure vendor agreements are understood. License compliance protects the business legally.
Monitor license usage across departments. Plan renewals. Train new employees on compliance rules.
IT Policies and Procedures
Clear IT policies guide employee behavior. Document acceptable use, security, and backup rules.
Update policies regularly to match technology changes. Make policies accessible to all staff.
Train employees on key procedures. Enforce policies consistently. Monitor compliance to detect gaps.
Adjust procedures based on feedback and incidents. Policies reduce errors and strengthen security.
Communicate policy changes promptly. Maintain version control for policy documents. Review procedures after incidents for improvements.
Internet and Web Security
Internet use brings risks if unmanaged. Block malicious websites and unsafe downloads. Use secure protocols for online transactions.
Monitor network traffic for anomalies. Educate staff on safe browsing habits.
Keep firewalls and security software updated. Limit access to high-risk sites. Test web security regularly.
Strong internet protection prevents breaches and downtime. Control remote access to internal systems.
Review security logs for unusual behavior. Update web security tools consistently.
Physical Security
IT systems need physical protection. Restrict access to server rooms and network equipment. Use locks, cameras, and alarms where necessary.
Control visitor access to sensitive areas. Keep hardware away from hazards like water or heat.
Label and organize cables and devices. Train staff on physical security rules.
Audit physical security periodically. Proper protection reduces theft and damage risks.
Install uninterruptible power supplies for critical equipment. Keep emergency contact information visible. Check doors and locks regularly.
Disaster Recovery Planning
Disasters can halt business operations. Create a detailed disaster recovery plan. Identify critical systems and data first.
Assign roles for response and recovery. Test the plan regularly through drills. Update plans based on lessons learned.
Include communication procedures for staff and clients. Coordinate with external IT services if needed. Preparedness reduces downtime after emergencies.
Document step-by-step recovery instructions. Review recovery priorities periodically. Ensure insurance covers IT-related losses.
Training and Awareness
Staff awareness is vital for IT security. Provide regular training on security practices. Teach safe email, internet, and device use.
Update training materials when technology changes. Test knowledge through exercises or quizzes.
Reinforce learning with reminders. Encourage reporting of suspicious activity. Measure the effectiveness of training programs.
Well-informed staff reduce risks significantly. Use real-world examples in training.
Schedule refresher sessions regularly. Reward staff for following best practices.
IT Asset Inventory
Keeping track of IT assets ensures efficiency. Maintain a list of all devices and software. Note purchase dates, warranties, and locations.
Update inventory whenever changes occur. Track usage and assignment to employees. Conduct regular audits for accuracy.
Dispose of obsolete items properly. Use inventory data to plan upgrades and purchases. An accurate IT inventory supports better management and budgeting.
Integrate the inventory with an information technology checklist for consistency. Use barcodes or asset tags for tracking. Ensure employees report changes immediately.
Vendor and Contract Management
Vendors provide critical IT services and products. Review contracts for service levels and costs.
Track renewal dates and payment terms. Assess vendor performance regularly. Maintain documentation of agreements.
Ensure vendors follow security and compliance rules. Communicate clearly about expectations and issues.
Have backup vendors for critical services. Proper vendor management prevents service gaps and legal issues.
Negotiate terms that support business needs. Monitor vendor compliance with contracts. Document lessons learned for future agreements.
There Is an Essential Information Technology Checklist for Businesses
A strong IT foundation supports business growth. Addressing networks, security, hardware, and policies is essential. Regular backups, training, and monitoring prevent major problems.
Cloud services and mobile management enhance flexibility. Disaster recovery and access controls protect critical data.
Following a structured information technology checklist ensures no area is overlooked. Implementing these points creates a safer, more efficient business environment.
For other topics, visit our blog page. We do have more!