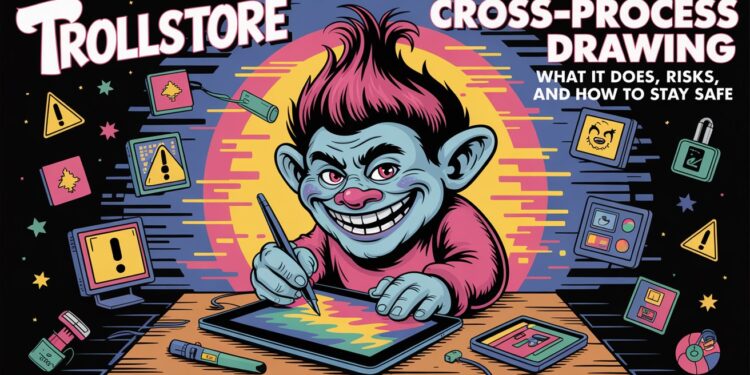
Trollstore Cross-Process Drawing lets an app display a persistent interface or overlay across other apps on iOS. This is not a simple widget — it bypasses normal app isolation and draws into the system UI space. TrollStore makes this possible by permanently signing apps in ways Apple’s normal App Store flow does not allow.
What is Trollstore Cross-Process Drawing?
Trollstore Cross-Process Drawing is a technique used by certain TrollStore-installed apps to render UI elements over other apps’ screens. Think of it as placing a live sticky note that can appear on top of any app — but created by a third-party app that has gained higher-than-normal privileges.
This is possible because TrollStore can install apps with powerful entitlements by exploiting a code-signing validation bug (often referred to as an AMFI/CoreTrust issue). In plain terms: TrollStore allows apps to carry permissions that normally only system components have.
Brief and direct: this is about visual control — showing overlays, drawing on screen regions, and injecting UI elements into the global display surface.
How it works — simple technical overview
- Permanent signing: TrollStore leverages a CoreTrust/AMFI signing bug so an app can be installed and treated as permanently signed on-device. That gives the app capabilities Apple usually reserves for system or enterprise software.
- Entitlements and privileges: With the right entitlements, an app can request or access system-level drawing APIs and render beyond its own sandboxed window. Those entitlements are the key enablers for Trollstore Cross-Process Drawing.
- Cross-process rendering: Once installed with elevated permissions, the app uses system hooks or privileged APIs to composite its visuals on top of other processes’ surfaces — effectively drawing across process boundaries. This is what people call cross-process drawing in practice.
Analogy: It’s like giving a single painter a ladder to reach every billboard in the city — they can change what everyone sees. That ladder is the special entitlement; the painter is the TrollStore app.
Practical uses — why people do this
- Persistent utilities: small overlays like always-on timers, quick controls, or accessibility helpers that sit on top of whatever app you’re using.
- Customization: visual themes, custom HUDs, or on-screen helpers that third-party launchers or tweak apps provide.
- Debugging and development tools: developers may use overlays to show logs, touch traces, or performance stats in real time across apps.
Real-life example: A music controller that stays visible while you use any other app — simple, useful, but it requires Trollstore Cross-Process Drawing style access to appear everywhere.
Practical note: many legitimate-looking uses exist, but the capability is powerful and must be treated as sensitive.
Security and privacy risks — be direct
- Visual spoofing risk: an overlay can mimic system dialogs or other app UIs and trick users into revealing sensitive data. “When you give an app the ability to draw across processes, you hand it control of what the user sees.” This is not theoretical — it’s exactly how attackers can craft convincing phishing overlays.
- Data exposure and interaction: cross-process drawing itself doesn’t necessarily read other apps’ data, but apps granted extra entitlements can often combine drawing with other privileged capabilities to capture input or intercept events. That combination raises the risk significantly.
- Stability and system impact: poorly written overlays can cause UI glitches, slowdowns, or crashes across multiple apps because they operate at a higher level in the rendering stack. Users can experience system instability if an overlay misbehaves.
Bottom line: powerful visuals = powerful risks. Treat any app offering cross-process overlays as potentially dangerous unless it comes from a vetted, trustworthy developer.
For deeper insights on how cybersecurity specialists evaluate system vulnerabilities and permission exploits like this, read our detailed piece on Experts Aigilbertwired, where industry experts break down real-world cases and modern iOS loopholes.
Who is affected — versions and scope
- TrollStore historically relied on CoreTrust/AMFI validation bugs to work; compatibility and install methods change as Apple patches vulnerabilities. Check current patch status before assuming availability.
- Security firms and researchers have repeatedly warned that TrollStore-style techniques affect multiple iOS versions until Apple patches the underlying code-signing or validation issues. Staying on the latest firmware is the usual defense for most users.
Clear fact: if your device is running a version affected by the underlying bug, TrollStore-style perma-signing and cross-process drawing are possible; if Apple patched the bug for your firmware, those methods are not available without a new exploit.
If you want to stay updated on the latest iOS patches and system changes that affect tools like TrollStore, check out our guide on New Software Versions Lcftechmods for complete version insights and compatibility notes.
How to recognize an app using Trollstore Cross-Process Drawing
- Unexpected overlays that look like system dialogs or offer controls while you’re inside other apps.
- New permanent apps installed that you didn’t get from the App Store.
- App behavior asking for unusual permissions, or offering global UI controls that persist across apps.
If you see these signs, treat them seriously: remove the app and consult trusted sources or forums for confirmation. Community discussions often surface when new TrollStore methods or overlays circulate.
How to protect yourself — quick practical steps
- Keep iOS updated. Apple patches code-signing and validation bugs; updates remove the ladder that TrollStore relies on.
- Avoid unofficial installs. Don’t sideload IPAs or install apps from untrusted sources that claim to give system-level features.
- Vet developers carefully. If you must use a tool from outside the store, confirm the project’s reputation (GitHub history, community reviews, security audits).
- Limit sensitive actions while overlays are active. If an overlay appears, avoid entering passwords or personal data until you confirm it’s safe.
Short, direct rule: no unknown trust = no global UI.
Responsible use — if you’re an advanced user or developer
- Use cross-process drawing only for clearly beneficial features (accessibility, developer tooling) and be transparent about what the overlay does and why it needs global access.
- Keep code minimal and audit logs to ensure overlays don’t capture or transmit sensitive inputs.
- “If you create a global helper, design it so the user can instantly tell it’s from you — visible branding and clear controls reduce spoofing risk.”
Responsible developers document entitlements, provide source code, and let the community audit builds before distribution.
Quick FAQ — short answers
- Is cross-process drawing the same as jailbreaking? Not necessarily. TrollStore works on non-jailbroken devices by exploiting signing bugs, so it’s different from a full jailbreak, but it provides some similar capabilities.
- Can an overlay read other app data directly? Drawing alone doesn’t guarantee data theft, but combined entitlements or other hooks can enable data capture. Assume risk and act accordingly.
- Should I install TrollStore apps for convenience? Only if you fully trust the developer and understand the risk. For most users, the App Store remains the safer source.

Final notes and a practical quote
Trollstore Cross-Process Drawing can enable genuinely useful enhancements, but it also hands a lot of power to an app. “Powerful overlays are useful only when the user explicitly trusts the hand that draws them.” If you value stability and privacy, treat any global-drawing app with caution and prefer vetted sources or system-provided features.